How to address the ‘cybersecurity skills gap’ at your business
It’s no secret that security fortification remains top of mind for IT leaders as we head into the next decade. For the second year in a row,...
The COVID-19 pandemic has forced a lot of businesses to reconsider a lot of things they once took for granted corporate leaders are taking a closer look at the ways people work, collaborate, and keep themselves safe and healthy. Also, in many cases, they’re reevaluating everything they thought they knew about security fortification.
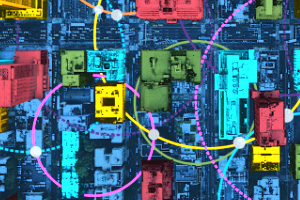
Previously, most companies had a security strategy that focused primarily on securing the networks they used on-premises. There was a routine process for securing your on-prem infrastructure and making sure you had control and visibility over who accessed your data, how, and when. But now, the paradigm is shifting. Because there are so many people all over the world working from home during COVID-19, companies must deal with the possibility of cyberattacks striking at individual remote locations. This challenge is a lot more complicated.
Network World recently reported on the results of the CSO Pandemic Impact Survey, which gauged how IT decision-makers were coping with the impact of COVID-19. The survey found that 61% of security and IT leaders are concerned about increasing cyberattacks targeting employees who work from home. And indeed, many of them have witnessed such an increase – 26% say they’ve seen greater volume, severity, and/or scope of attacks since the middle of March.
These security breaches can come in all different forms. Phishing attacks are more prevalent now, as employees working from home are often juggling multiple email accounts for business and personal use, and they can easily open untrustworthy emails from outside the organization. Similarly, ransomware attacks are a common vulnerability for companies to be aware of. There’s also the potential for widespread distributed denial of service (DDoS) attacks, which can be particularly harmful when your remote workers attempt to access the same resources at the same time.
Working from home is the new normal, and it’s crucial that companies adjust their security plans accordingly. They should ensure that all anti-malware software is up to date. Additionally, they should be scheduling complete data backups on a regular basis, so that if any sort of cyberattack does happen, business continuity isn’t affected. Lastly, it’s incumbent upon IT managers to provide security training for everyone, ensuring that employees know how to keep their data secure, when they’re remote.
At Zones, we specialize in keeping your data safe. We have a series of Security Assessments we can use to evaluate your current IT infrastructure and identify areas where you can improve. These are rapidly changing times in business, and cybersecurity needs to be prioritized by all organizations – large and small.
Want to learn more about the Security Fortification offerings we have at Zones? Read on…


It’s no secret that security fortification remains top of mind for IT leaders as we head into the next decade. For the second year in a row,...

The growth of modern technology has had a major impact over the last couple of decades in education, especially at the higher-ed level. Among the...

As you close the book on 2019 and begin looking ahead to 2020, you’ve probably set a couple of resolutions for yourself for the new year. Maybe you...